So many people recommend ‘The Cuckoo’s Egg’ as a must-read for information security professionals. For those in the dark, the book follows the author Cliff Stoll tracking unauthorised access to the US Lawrence Berkeley National Laboratory computer network in the late 1980s.
The book itself is an engaging and fascinating account of a low-tech attacker (by today’s standards) penetrating various networks across the US and the low-tech defender tracking his activities. Cliff’s use of 1980s technology to frustrate and degrade the attacker is sometimes hilarious (e.g. jangling his keys to literally introduce random noise on the wire).
Some of the quotes I took away from the book could be said today without any question:
The hacker didn’t succeed through sophistication. Rather he poked at obvious places, trying to enter through unlocked doors. Persistence, not wizardry, let him through. ‘The Cuckoo’s Egg’, Chapter 20, p. 126.
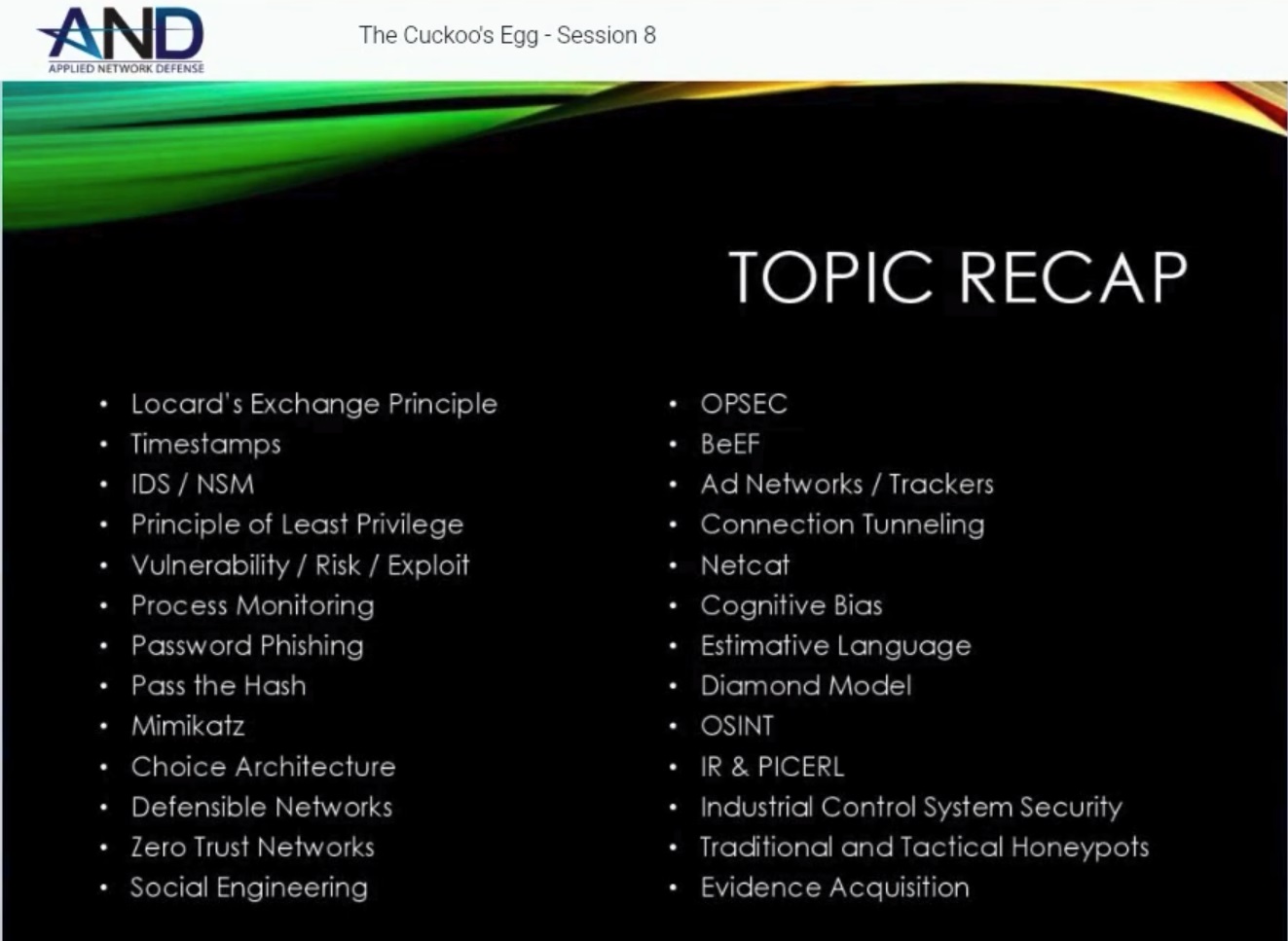
This is the most amazing part about the Cuckoo’s Egg: the majority of the principles that Cliff Stoll used to monitor, analyse, and eventually track down his adversary are the same today. The parallels are so stark that Chris Sanders put together an eight week course following the book and drawing out the information security principles. Chris bills the course as an introduction to information security; and while that is accurate, it’s also a great way to deeply explore the book and its legacy today.
The course covers a wide range of modern topics which Chris summarises in the final week:
For those of us who often get the question: ‘What do you do all day?’ or ‘Can you hack my Facebook account?’ or even better ‘How do I get to do your job?’ I’d recommend giving him/her a copy of the book and then pointing them to the course which is generously available for free on Vimeo.
For all of Chris’s hard work, I have to plug his books and courses and thank him for his work.
I always love book recommendations. Here are mine (so far), please let me know if you have any for me at @mattnotmax or [email protected].
