Great sources of DFIR information are endless: books, blogs, repositories, Twitter, lectures, conferences, and journals. One of the hardest skills I am yet to master is transferring this huge amount of information into digestible and searchable chunks. At the moment my ‘system’ consists mainly of a stack of printouts, endless Twitter bookmarks, 75 open Chrome tabs, and sticky notes with Excel formulae (generally different ways to convert Unix epochs to a readable format en mass…).
So, I thought to change tack from my usual path and try mind mapping. It was inspired by a tweet from Jack Crook (@jackcr)
If you want to start dynamically detecting beacon traffic, it may help to define characteristics of a beacon. Not all will look the same, but will likely share some similarities with others. Can you cluster characteristics and surface unknown? #ThreatHunting #DFIR pic.twitter.com/OhRqr7F3O0
— Jack Crook (@jackcr) May 4, 2018
My initial task was a Volatility mind map. The result is this first cut of a high-level command reference:
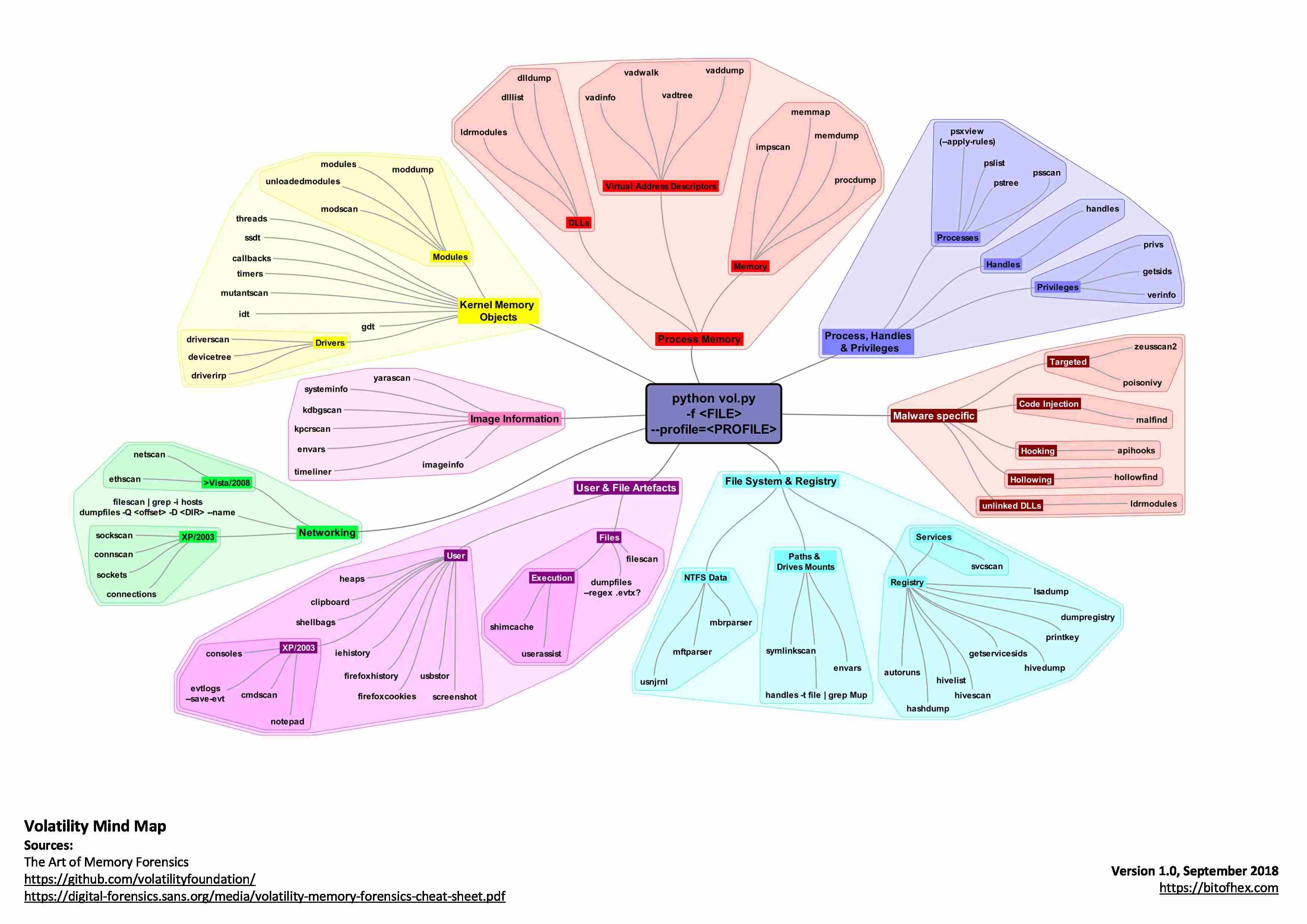
The Volatility framework is so large and memory forensics so vast, I’ll probably expand this so each node has key command switches and contextual summaries, but as I work through the book it’s been a great way to really think about how different commands relate to one another. There are endless ways that it could also be visualised, which makes mind mapping such an interesting and memorable way of learning.
A higher quality PDF copy is available on GitHub. While it’s available, I highly encourage you to develop your own mind map: as with all ‘cheat sheets’ it’s not really the end result, but the process of synthesising information into smaller chunks that makes the system work.
If you’ve got a way to learn, study, remember, or reference please let me know at [email protected] or via Twitter (which I’ll probably just bookmark) at @mattnotmax.
